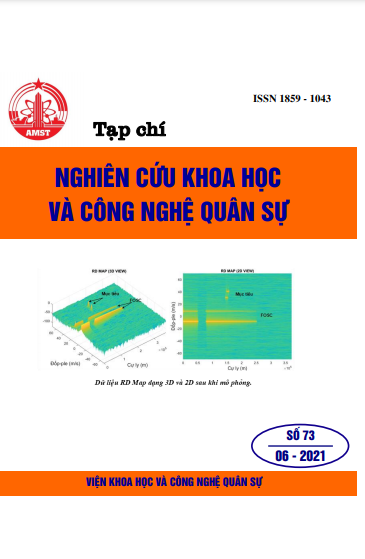
ABOUT A HIGH PERFORMANCE AUTHENTICATED ENCRYPTION ALGORITHM
299 viewsKeywords:
Encryption algorithm; Authenticated Encryption AE; Decryption; Duplex constructionAbstract
In the rapidly growing era of technology 4.0, cybercrime is also becoming more sophisticated. Hackers can easily circumvent security measures and gain access to sensitive personal data. On the other hand, the authentication cipher structures used over the years based on symmetric block ciphers have increasingly revealed many limitations in performance, processing speed due to the amount of information that needs to be processed, and the amount of information be verified increasing. The paper presents a high-performance authentication encryption algorithm based on a duplex design with appropriate security parameters using permutations that can be used to protect information with a degree of confidentiality and information that has varying degrees of sensitivity.
References
[1]. D. Stinson, Cryptography, “Theory and Practice”. CRC Press, LLC, 1995.
[2]. M. Bellare, C. Namprempre, "Authenticated encryption: Relations among notions and analysis of thegeneńc composition paradigm, Journal of Cryptology”, vol. 21, no. 4, 2008.
[3]. G. Bertoni, J. Deamen, M. Peeters, G. Van Assche, "Cryptographic sponge functions", January 2015,http://sponge.noekeon.org.
[4]. M.Borowski, ''The sponge construction as a source of secure cryptographic primitives", Military Cornmunication Conference, France, 2018.
[5]. M.Borowski, M. Leśniewicz, R. Wicik, MGrzonkowski, "Generation of random keys for cryptographic systerns", Annales UMCS lnformatica, AIXII, 3 (2016).
[6]. I. Dinur, O. Dunkelman, A Shamir, "Self differential crypt analysis ofup to 5 rounds of SHA-3",http://eprintiacr.org/2012/672.pdf.
[7]. M. Kutyłowski, WB. Strothmann, “Lý thuyết mật mã và thực hành đảm bảo an toàn các hệ thống máy tính”, Nhà xuất bản Read Me, Warsawa 1998.
[8]. D. KKhovratovich, "Keywrappingwith fixedpermutation", http://eprint.iacr.org/2013/145.pdf.
[9]. V. Gligor, P. Donescu, "Fast encryption and authentication: XCBC encryption and XECB authentication modes", FSE 2012, LNCS 2355, Springer-V er lag, 2012.
[10]. M. Duan, X. Lai, "Improved zero-sum distinguisher for full round K.eccak-fpermutation", 2012,http://eprintiacr.org/ 2012/ 023.pdf.
[11]. NIST, "Special Publication 800-38D, Recornmendationfor Błock Cipher Modes of Operation:Galois/Counter Mode (GCM) and GMAC", 2009.
[12]. Jovanovic P., Luykx A., Mennink B, “Beyond 2c/2 security in sponge-based authenticated encryption modes”, http://eprint.iacr.org/2016/373.pdf.
[13]. P. Rogaway, "Authenticated-encryption with associated-data", ACM Conference on Computer and Cornmunications Security (CCS-9), ACM Press, 2005.
[14]. P. Rogaway, M. Bellare, J. Black, ''OCB: A block cipher mode of operation for efficient authenticated encryption", ACM Transactions on lnformation and System Security, 2006.
[15]. R. Gliwa, “Uwierzytelnione szyfrowanie wspecjalnych sieciach telekomunikacyjnych", Rozprawadoktorska, Wojskowa Akademia Techniczna, WydziałElektroniki, 2016.